Fingerprints are unique. Everyone has one. Permanent throughout life, etc. There are numerous reasons why they are used by various officials, government agencies, and forensic sciences.
Apart from this, there are many applications of fingerprints that we see in our daily lives. I am going to list down the major uses of fingerprint and other fingerprinting technologies and security systems in our life that makes it more secure than ever.
1. Your Perfect Grip

Fingerprints have friction ridges that extend from palm base to tip of fingers. These friction ridges are not only unique but they add extra grip. Hence, resist slipping and avoid slipping when you’re holding a smooth surface.
Similarly, the ridge details on your feet of the sole also prevent you from slipping on the wet floor.
Example: For holding instruments such as glasses of water.
2. A Better Solution for Law Enforcement

A major part of forensic science is to evaluate the evidence and link it back to suspects or perpetrators. Here, fingerprints work like a charm.
Most crime scenes usually have fingerprints. These fingermarks first need to be developed by investigators and then compared with the finger templates stored in the database.
Once the information is matched to the alleged person, he/she can’t deny their presence at the crime scene. Moreover, fingerprints in forensics also facilitate a faster investigation and comparison of one-to-one fingerprints than other evidence. Check out the one to one comparison method for fingerprints at school.
Example:
- Identifying persons that are at the crime scene.
- Validate a person by matching fingerprints from the scene and from suspects.
3. Verify Your Identity

When you’re claiming someone, you have to prove your identity. This can be anything– from a driver’s license to National Id card. In all this, government agencies may ask you to verify yourself using fingerprints.
The FBI also uses fingerprints as the authentication means. You have to fill out the FBI fingerprint card that they later processed and add to their database.
And once the government or FBI need to verify your identity, they use your stored fingerprint data to match with the current input fingerprint.
Example: Verify yourself by authenticating with the fingerprint in your database.
4. Validate you in Background Checks
You may finally get a job. Congratulations! But in many government and commercial agencies, there is an extra step of a background check.
This may or may not include verification of your information by fingerprinting biometric authentication.
In many developed countries, the government has a centralized criminal database which usually includes fingerprints. So, your fingerprint may be fed into the system to check any criminal history. If nothing is found, your data or record typically discards after returning the result to agencies.
Example: All government jobs in the USA need background checks and one part is validated by fingerprints.
5. You will be Easily Traced
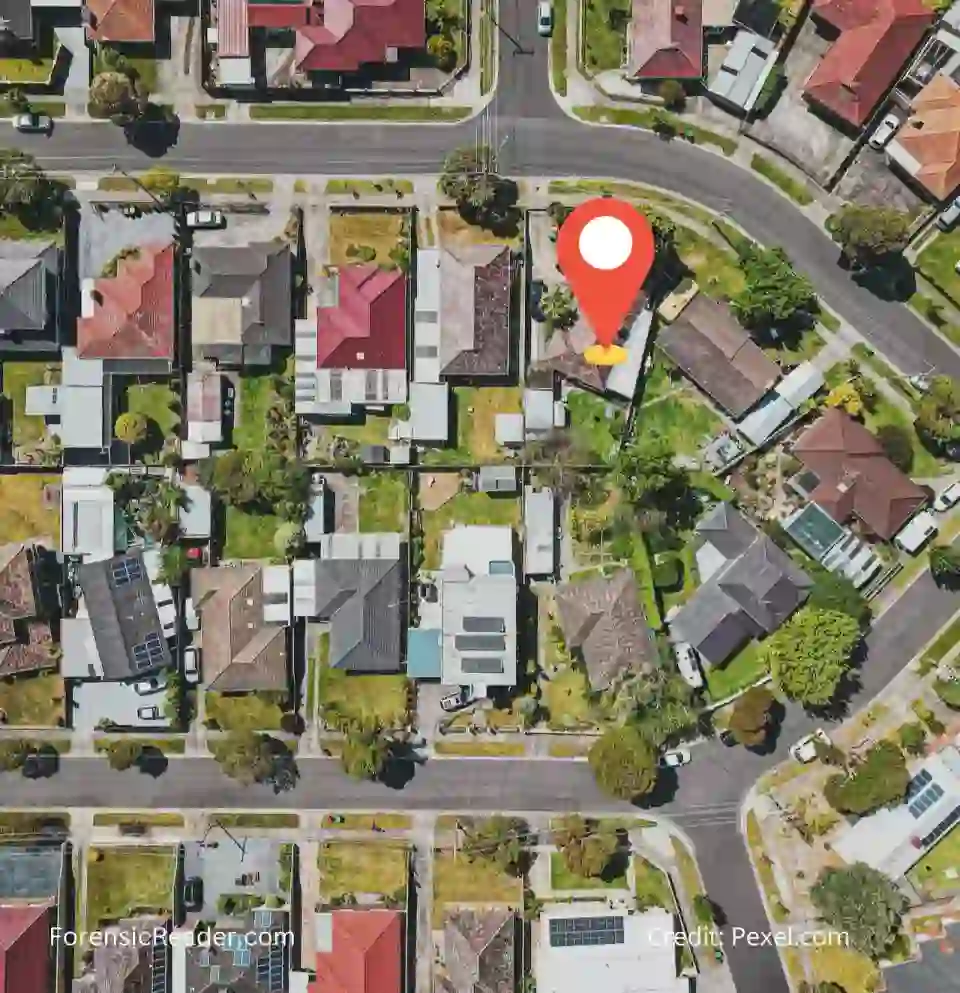
Surveillance need not be the application of monitoring cameras. They can be done with fingerprints with similar accuracy.
If you’re working in a firm that has a fingerprint-based authentication system, then this data is used to find your presence in a certain time period.
However, there are various ways to get away from the fingerprint authentication system which is the major drawback.
Example: System can also be tweaked to send alerts to officials when a person uses their prints to log in.
6. Identifying Risk Traveler Profiles

Travelers traveling in or out of a country are easily managed by studying their passports. However, many countries have friendly borders that allow safe passage without passports.
In those cases, a centralized biometric system is needed that tracks their movements and even identifies them. The system is usually setup as traverse security checkpoints for security inspections.
For this fingerprint along with other biometric technologies such as facial and iris recognition is used at the border. With proper centralized data and monitoring, safe screening for every traveler could be established.
Example: Person A traveling to California and at the state border using a fingerprint, he had a criminal history. So, police officers check his vehicle and take him into custody.
7. Who is Behind it?– Fraud Prevention
In the USA, one of the common frauds is identity fraud. When a person pertains to someone and uses their identity for their benefit it is called Identity fraud.
For preventing it, biometric fingerprints come in handy. So, he/she may need to verify themselves before submitting or performing their desired work or accessing sensitive information.
Many online password manager applications nowadays start using fingerprint authentication systems to make sure no one else accesses your passwords.
Example: Use of two-factor authentication in financial transactions such as fingerprint followed by OTP or vice versa.
8. Your Way In– Physical Access Control

Physical fingerprint authentication devices at doorsteps become common. These automated fingerprint devices identify or verify the identity of a person before letting them access an area.
This works by capturing fingerprints from the person and then comparing them with the local fingerprint information stored in the database. The system doesn’t need any sophisticated classification system and tools that are used for identification by the government.
Fingerprint also validates a successful login to a remote location to accurately identify a legitimate user.
Example: Companies, govt agencies, goal clubs memberships, etc now start using fingerprint technology to provide access to their employers and members.
Read More: How to Compare Fingerprints at Home? A Simple Guide by Forensic Expert.
9. Yes! I’m Present– Time and Attendance

In Public areas such as colleges and high schools, you don’t need physical access to roam around as a student. However, for the facility, you may see a fingerprint device that not only registered the attendance but also the time.
This not only helps in maintaining the attendance sheet of the facility but also their timing and punctuality. This information can be used to ensure the work hours and payroll of the employees.
Example: I have a gym membership that uses a fingerprint-based attendance sheet stating when I enter or leave the gym.
10. My Financial Safe– Financial and Banking Activity

Many financial apps on your android and apple phones use an authentication tool including keycards, PIN numbers, and passcode to ensure your validity.
The main drawback is that anyone who knows these passcodes can enter a financial app and make transactions. But recently, most financial apps and banking systems require additional fingerprint authentication. Even some mobile apps start using fingerprints as authentication.
This does not eliminate the chance of invalid transactions made by anyone who knows your code. So, it binds you to safer financial transactions.
Example: Inbuilt fingerprint sensors authenticate the fingerprint first and then let you use their financial app or e-commerce store.
11. My Safest Safe– Asset Protection

Recently, I purchased a digitally wifi-enabled safe that has a fingerprint biometric system. It has three ways to access: one is by entering the code, the second by a key, and the third and fastest one is the fingerprint.
Like this, there are a lot of safes that use fingerprint recognition systems to protect your sensitive materials. They are now becoming common. However, there are various videos on youtube that show how these safes can be fooled easily but again it is very hard and needs a lot of effort.
Example: Digital safes that open with a fingerprint and also notify you via app or email that someone opens your safe.
12. A Better Future– Medical research

There are some medical conditions related to fingerprints including Adermatoglyphia, where persons have no ridge patterns. Various research papers are not only evolving for their development but also their links to genetics.
Recent studies point out that one of the factors that affect fingerprint uniqueness is genetics. Many researchers also investigate the effects of diseases on the fingerprints and their development when the infant was in the womb of the mother.
Examples: Fingerprint Patterns in Alzheimer’s Disease by Herman J. Weinreb, MD.
13. Baby is Born– Hospital and Healthcare Facilities

Most hospitals have a management system to handle newborns. For this, they usually have a number tag and a palm and sole print registration.
This ensures that the right newborn reaches the right parents after a preliminarily caring unit (also called Neonatal Intensive Care Unit.)
When a dispute is called by parents, they have palm and sole prints to prove and present their theory.
Example: Two Babies Discovered Switched in Hospital 20 Years Ago
14. You don’t Need Keys for Smart Home

There is a new trend of smart homes. Many companies start making innovative products around it. One of the products is the fingerprint security system. The most common one is the fingerprint door system which doesn’t need a key to open your house door.
So, if you have a bigger family, say 6-7 members, you don’t need to make seven separate keys for them. Just add their fingerprints in the system, and use a keyless way to enter in the house.
Example: The most common smart home fingerprint system is by Veise Store.
15. Keyless Entry in Car– Automotive Industry

Many car manufactures added biometric authentication to their car system. Some use an android or apple app to start the car and some use a physical fingerprint touch button on car doors to open the car.
These cars do not need a physical key to open and ignite car engines. However, in case, the battery is damaged or has some technical failures, the user does need the physical key to open it.
Read More: 11 Reasons Why Fingerprints Used for Identification in Forensic Science

FR Author Group at ForensicReader is a team of Forensic experts and scholars having B.Sc, M.Sc, or Doctorate( Ph.D.) degrees in Forensic Science. We published on topics on fingerprints, questioned documents, forensic medicine, toxicology, physical evidence, and related case studies. Know More.